The volume of counterfeited goods sold online is estimated in over 500 billion dollars a year and one product out of 7 sold online is counterfeited. It is an alarming phenomenon constantly rising.
by Francesco Chimini (Partner – European Patent Attorney of Jacobacci & Partners) and Marco Rollando (CEO of GriffeShield S.r.l)
 We all know Internet on one hand constitutes a great opportunity to develop one’s own business but, on the other hand, an as relevant menace that jeopardizes companies’ competitive edges. The same web features that favour the legitimate trade are finally precious for the counterfeiting chain, too. According to a study by Indicam, in particular, the most responsible characteristics for its distorted use are the offer anonymity or the simple authenticity simulation, the possibility of choosing among a very broad typology of virtual stores, the transaction security, in both economic and distributive–logistic terms; in fact, the meshes of the net are generally large enough to allow the passage of the small shipments that concern final consumers.
We all know Internet on one hand constitutes a great opportunity to develop one’s own business but, on the other hand, an as relevant menace that jeopardizes companies’ competitive edges. The same web features that favour the legitimate trade are finally precious for the counterfeiting chain, too. According to a study by Indicam, in particular, the most responsible characteristics for its distorted use are the offer anonymity or the simple authenticity simulation, the possibility of choosing among a very broad typology of virtual stores, the transaction security, in both economic and distributive–logistic terms; in fact, the meshes of the net are generally large enough to allow the passage of the small shipments that concern final consumers.
Online counterfeiting numbers in the world are relevant and constantly rising:
– the volume of counterfeited goods sold in the world is estimated in over 500 billion dollars a year;
– the counterfeited goods sold online in the world are equal to 1 product every 7 genuine products;
– the damages caused by digital piracy in the world are estimated in over 85 billion dollars yearly.
The products most counterfeited through Internet include electronic products, telecommunication devices, and their spare parts.
The counterfeiting of electronic products constitutes over 25% of overall counterfeited products in the world. Just in Italy, according to Censis reports for the Ministry of Economic Development, currently the counterfeiting of electronic products has a market worth over 1.5 billion Euros.
However, what are, more in detail, the illicit activities that exploit the web? We can summarize such problems as follows:
• Abusive Internet domains
• Unauthorized use of brands
• Counterfeiting of products
• Unfair competition
• Copyright violations
• Online reputation damages
• Frauds and violations of cyber-security
The ambits where it is possible to identify these illicit activities are, in particular:
• Internet domain registers
• Open web
• Internet websites
• Social networks
• P2P networks
• Mobile APP
• Dark web
The problem is so relevant and felt that more than 98% of big companies in the world, in all sectors, today feel the need of implementing an online protection strategy for their brands and products. The targets that such online protection fixes, and in many cases allows reaching, are manifold, such as:
• Preserving the integrity of the brand and of the intellectual property
• Preserving the efficacy of investments in marketing
• Protecting the online brand reputation
• Reducing turnover losses caused by online counterfeiting
• Protecting consumers’ confidence
• Avoiding the unfair diversion of customers
However, in what do online protection strategies consist?
If, on one hand, new information technologies allow counterfeiters to sell more and more easily through the web, on the other hand such technologies, and especially software based on artificial intelligence, permit to monitor the web and to identify automatically each abuse, product counterfeiting included.
Therefore, in recent years, companies specialized in offering online anti-counterfeiting services have been established and they basically operate with the following methodology:
– Detection of infringements on the web;
– Analysis and cataloguing of information
– Problem-solving, through an automatic reporting of validated abuses to eliminate or to minimize illicit activities, according to the laws in force.
It is clear that the identification, but especially the removal of the abuse, need the presence of a team who, besides IT experts, can rely on the support of consultants in industrial property protection and in international law in Internet.
In particular, it is first worth specifying that, to consider illicit an unauthorized online sale activity and then to remove it efficaciously, it is necessary there is an infringement of intellectual property rights to the detriment of the company that intends to contrast the online counterfeiting. Therefore, at the base of the repression strategy of the illicit activity, there should be a protection strategy of the company’s immaterial assets, essentially based on registered industrial property rights. Let us remind that such rights consist in:
– registered trademarks, which protect the distinguishing features of the company, or products and services;
– patents of industrial invention or by utility model, which protect technical aspects of a product or proceeding;
– registered designs or models, which protect the aesthetical aspect of a product or of one of its parts, user graphic interfaces included.
In addition to these registered industrial property rights, there are other intellectual property rights that do not necessarily need a registration and can be anyway used as legal base to remove an infringement identified on the web. Such unregistered rights are the following:
– copyright, which protects the intellectual property, software included;
– industrial secrets, or know-how;
– unregistered designs or models, which are anyway protected in the European Union for a period of three years since their first divulgation;
– unregistered distinguishing features (trademarks, domain names and so on but only if they have gained ultra-local notoriety).
Finally, online sale activities can be considered illicit if they belong to unfair competition acts, in other words, in particular, if those executing them, “use names or distinguishing features apt for generating confusion with the names or distinguishing features lawfully used by others, or slavishly imitate the products by a competitor, or perform, with any other means, acts capable of creating confusion with the products and the activity of a competitor” (Art.2958, c.1 of the Civil Code).
Given that, let us see more in detail how it is possible to contrast the online counterfeiting, making the example of a supplier of this service and the experience of a company that is availing itself of that.
A company that offers a highly innovative and efficacious online anti-counterfeiting service is the Italian company Griffeshield srl (www.griffeshield.com). Its software platform is based on an artificial intelligence engine that uses various proprietary technologies such as the image comparison and the semantic analysis to identify abusive contents and counterfeited products in the billions of Internet pages present worldwide and in all web channels like Internet sites, marketplaces, social networks and APPs. The system speed is guaranteed by Ishtar II supercomputer in which the platform runs.

If the traditional procedure of online counterfeiting contrast implies the involvement of a law firm – sometimes also in collaboration with a foreign law firm headquartered in the Country where the counterfeiter is supposed to reside, which examines any single illicit act and then draws up and sends a letter of formal notice, often addressing more subjects of the counterfeiting chain, with costs amounting to even several thousand Euros -, by using the IT/legal platform by Griffeshield the abuse removal is automatically executed through the artificial intelligence engine. The engine searches for contact details of all involved subjects (owners, providers, platforms and legal teams) for any infringement and it processes a reporting protocol in language, including the required Intellectual Property titles, the infringement proof, technical data, the abuse description, violated laws and the specific know how concerning the case. Moreover, it sends reports to search engines, Internet control organizations, police on Internet and credit card systems. Depending on the reporting result, the system proceeds with different techniques to maximise results. If, for instance, a Website removed from the system is then displaced (it changes provider), the platform automatically follows it and will remove it again. Otherwise, if an Internet provider does not collaborate, techniques (even at higher net levels) are used to demonstrate the bad faith and to undertake actions.
Due to such automated system, the cost for each removal amounts to few Euros! Moreover, the company can entrust the service supplier with almost the whole online protection activity and focus its resources on the management of high-level problems. The software platform allows tracing and controlling monitoring/analysis/removal processes of Internet abuses in simplified manner, also by figures in the company without specific IT/legal skills.
Let us see now in detail how some anti-counterfeiting actions are implemented.
Abusive internet domain monitoring. Internet domains whose names contain company’s trademarks or names of products, both precise and similar, are searched and monitored. The domain search occurs in all active world extensions. The search includes also the domains registered with IDN characters, that is to say in the foreign languages enabled to registration for each extension.
Monitoring of abusive brand use in Internet. The unauthorized use on Internet of the company’s brand is searched, identifying similar brands, too. The control is both textual and graphic. The search ambit can include: open web, social networks, blogs and forums, e-commerce portals, mobile applications, P2P networks, dark web.
Monitoring of unfair competition in Internet. It is searched the use in unfair competition on Internet of the brand name, of best-selling products, of key writings and words of company’s property. The verification in Internet pages is textual on the plain text, on the code, and on keywords.
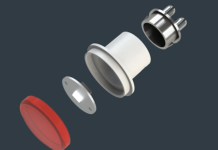
Monitoring of counterfeiting in Internet. They are searched in Internet the products on sale suspected of counterfeiting as they include designs /models/patents regarding the company’s original products. The check is both textual and graphic in Internet pages. Comparison data are based on information concerning designs/models/patents and product features preliminarily provided by the company, as well as associative search algorithms with GriffeShield proprietary technology.
Monitoring of copyright infringement in Internet. They are searched in Internet the elements suspected of copyright infringement versus the works of an author indicated by the company. The verification is textual, graphic, audio, video, and software applicative. Comparison data are based on the information preliminarily provided by the company, as well as associative search algorithms.
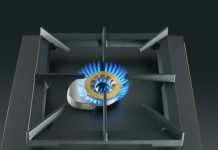
The most counterfeited electronic products certainly include telephony and IT, household appliances, remote controls, domotics devices and many others.
One of the biggest reality in the world in the sector of home automation, home security and smart home, Nice multinational company, is using the Griffeshield solution with high satisfaction to contrast the phenomenon of the online counterfeiting of its products, especially of transmitters to control automations.
As we can notice in the chart shown below, the geographical distribution of menaces concerns almost the entire world and not only China, which anyway remains the provenience Country of the vast majority of counterfeiting. The picture on the right shows the corporate brand filing strategy that, as we can notice, well suits the geographical counterfeiting distribution.

When the product counterfeiter uses the corporate registered brand, in fact, the marketplace manager generally closes the web page immediately, as soon as he receives the report from Griffeshield. However, counterfeiters use also more sophisticated strategies. They propose, for instance, similar products, or even identical to the original, but without the company’s brand or with a different brand. In these cases, the possibility of using the legal instrument of the registered design, to make the abusive web page be removed quickly, is highly advantageous.
 The image shows an example of this situation. It is shown a web page of Alibaba marketplace, where they sell a transmitter equal to the original but without the manufacturer’s logo.
The image shows an example of this situation. It is shown a web page of Alibaba marketplace, where they sell a transmitter equal to the original but without the manufacturer’s logo.
In this case, it was possible to identify the counterfeiting through the image comparison algorithm of the platform, which succeeds in detecting identical or similar objects through their design, surpassing the limits of the search by keywords that is typical of search engines and of electronic trade platforms. The image comparison algorithm is based on geometrical comparisons among vectorized product images and comparisons of their textures. An already recognized image vector helps then the system in improving the counterfeited item detection.
Once detected the counterfeiting, thanks to the exclusive right provided by the transmitter design registration it was possible to close the web pages immediately.
In the first 6 months of service, the online product counterfeiting was reduced by 68% on a global scale, with a market equivalent of some million Euros/year. 3,100 web pages were closed.
Worth noticing that Griffeshield platform allows identifying not only counterfeited goods but also unauthorized sales of original products.
The companies that have equipped themselves with anti-counterfeiting services, like Griffeshield one, have an undoubted advantage on the market because the protection in Internet they obtain indirectly determines a recovery of turnover and image towards customers and end users, besides efficaciously exploiting their own industrial and intellectual property rights.